公開ベータプログラム(Public Beta Program)が開始された
debian9で試してみる
インストール
root@debian9:/usr/local/src# apt-get install git ... root@debian9:/usr/local/src# git clone https://github.com/letsencrypt/letsencrypt ... root@debian9:/usr/local/src# cd letsencrypt
Let’s Encrypt クライアントソフトウェアを実行できる環境か確認する
確認が完了するとLet’s Encrypt のヘルプが表示される
どうもDebian系がオススメの模様(AmazonLinuxは現状experimentalらしい)
root@debian9:/usr/local/src/letsencrypt# ./letsencrypt-auto --help ... apt-get install -y --no-install-recommends git python python-dev virtualenv python-virtualenv gcc dialog libaugeas0 libssl-dev libffi-dev ca-certificates というコマンドが実行された ... letsencrypt [SUBCOMMAND] [options] [-d domain] [-d domain] ... The Let's Encrypt agent can obtain and install HTTPS/TLS/SSL certificates. By default, it will attempt to use a webserver both for obtaining and installing the cert. Major SUBCOMMANDS are: (default) run Obtain & install a cert in your current webserver certonly Obtain cert, but do not install it (aka "auth") install Install a previously obtained cert in a server revoke Revoke a previously obtained certificate rollback Rollback server configuration changes made during install config_changes Show changes made to server config during installation plugins Display information about installed plugins ...
nginxの証明書を作成する
以下をnginxのサイト設定に追記
location '/.well-known/acme-challenge' {
default_type "text/plain";
root /tmp/letsencrypt-auto;
}
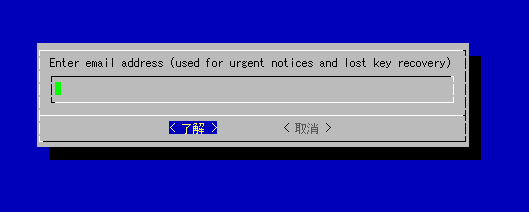
root@debian9:/home/shimizu# export DOMAIN="-d tech.akat.info -d akat.info" root@debian9:/home/shimizu# export DIR=/tmp/letsencrypt-auto root@debian9:/home/shimizu# mkdir -p $DIR && /usr/local/src/letsencrypt/letsencrypt-auto certonly --server https://acme-v01.api.letsencrypt.org/directory -a webroot --webroot-path=$DIR --agree-tos $DOMAIN Updating letsencrypt and virtual environment dependencies....... Running with virtualenv: /root/.local/share/letsencrypt/bin/letsencrypt certonly --server https://acme-v01.api.letsencrypt.org/directory -a webroot --webroot-path=/tmp/letsencrypt-auto --agree-tos -d tech.akat.info -d akat.info IMPORTANT NOTES: - Congratulations! Your certificate and chain have been saved at /etc/letsencrypt/live/tech.akat.info/fullchain.pem. Your cert will expire on 2016-03-08. To obtain a new version of the certificate in the future, simply run Let's Encrypt again. - If like Let's Encrypt, please consider supporting our work by: Donating to ISRG / Let's Encrypt: https://letsencrypt.org/donate Donating to EFF: https://eff.org/donate-le root@debian9:/home/shimizu# ls /etc/letsencrypt/live/tech.akat.info/ cert.pem chain.pem fullchain.pem privkey.pem
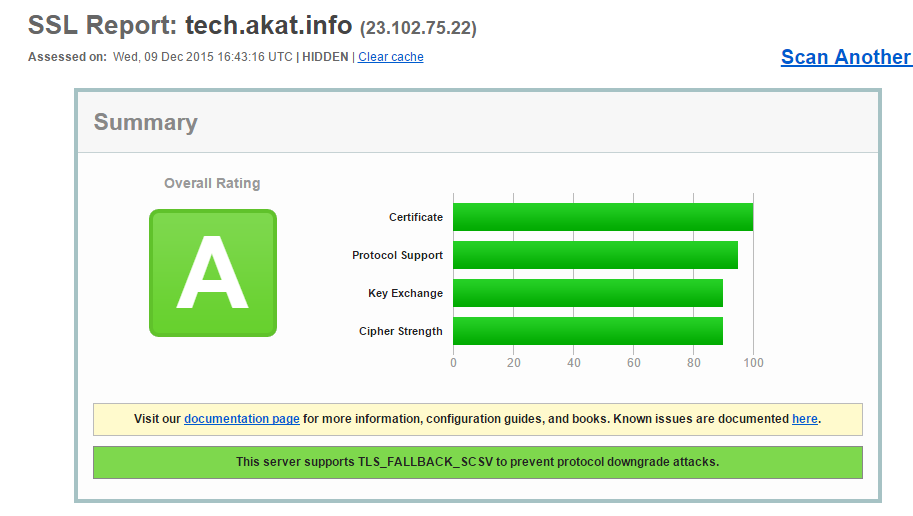
SSL証明書を設置する
SSL設定についてはMozilla SSL Configuration Generatorを利用した
listen 443 ssl; # certs sent to the client in SERVER HELLO are concatenated in ssl_certificate ssl_certificate /etc/letsencrypt/live/akat.info/fullchain.pem; ssl_certificate_key /etc/letsencrypt/live/akat.info/privkey.pem; ssl_session_timeout 1d; ssl_session_cache shared:SSL:50m; ssl_session_tickets off; # Diffie-Hellman parameter for DHE ciphersuites, recommended 2048 bits ssl_dhparam /etc/ssl/private/dhparam.pem; # intermediate configuration. tweak to your needs. ssl_protocols TLSv1 TLSv1.1 TLSv1.2; ssl_ciphers 'ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES256-GCM-SHA384:DHE-RSA-AES128-GCM-SHA256:DHE-DSS-AES128-GCM-SHA256:kEDH+AESGCM:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA384:ECDHE-RSA-AES256-SHA:ECDHE-ECDSA-AES256-SHA:DHE-RSA-AES128-SHA256:DHE-RSA-AES128-SHA:DHE-DSS-AES128-SHA256:DHE-RSA-AES256-SHA256:DHE-DSS-AES256-SHA:DHE-RSA-AES256-SHA:ECDHE-RSA-DES-CBC3-SHA:ECDHE-ECDSA-DES-CBC3-SHA:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128-SHA256:AES256-SHA256:AES128-SHA:AES256-SHA:AES:CAMELLIA:DES-CBC3-SHA:!aNULL:!eNULL:!EXPORT:!DES:!RC4:!MD5:!PSK:!aECDH:!EDH-DSS-DES-CBC3-SHA:!EDH-RSA-DES-CBC3-SHA:!KRB5-DES-CBC3-SHA'; ssl_prefer_server_ciphers on;
困ったときの証明書確認方法
root@debian9:/home/shimizu# openssl x509 -text -noout -in /etc/letsencrypt/live/tech.akat.info/fullchain.pem
Certificate:
Data:
Version: 3 (0x2)
Serial Number:
01:10:86:c4:52:70:57:06:82:e6:bc:1a:ee:bc:ba:1b:1e:28
Signature Algorithm: sha256WithRSAEncryption
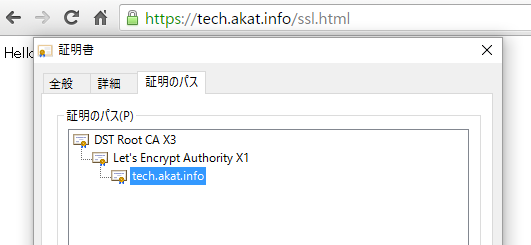
Issuer: C=US, O=Let's Encrypt, CN=Let's Encrypt Authority X1
Validity
Not Before: Dec 9 15:13:00 2015 GMT
Not After : Mar 8 15:13:00 2016 GMT
Subject: CN=tech.akat.info
...
root@debian9:/home/shimizu# openssl s_client -connect tech.akat.info:443 -showcerts
### s:証明書情報、i:証明書発行者情報 ###
...
Certificate chain
0 s:/CN=tech.akat.info
i:/C=US/O=Let's Encrypt/CN=Let's Encrypt Authority X1
...
参考URL
Let’s Encrypt の使い方
How It Works
One-line certificate generation/renews with Letsencrypt and nginx